Getting Value from the Cloud
There are more options for purchasing Cloud-based supply chain software applications than ever. The key is realizing the value and savings promised by Cloud vendors.
Open any business publication and an IT or supply chain manager is likely to find an ad like the one from Microsoft Cloud claiming: “This Cloud opens doors of opportunity.”
The promise of the Cloud, according to Microsoft Cloud, is that it frees up cash by reducing “the need for infrastructure and management.” Costly licensing fees and implementation costs are replaced by subscriptions; gone is the expense associated with maintaining on-site servers and managing upgrades; and everyone is always working with the latest version of the applications.
But, when it comes to the reality of sourcing Cloud services for procurement professionals, is it really as simple as replacing existing applications with Cloud applications? What are the questions a supply chain organization should consider to get value from the Cloud? And, what are the steps that a supply chain manager can follow to better direct their Cloud sourcing dollars in order to gain superior value?
Those are some of the questions we sought to answer in a recently concluded CAPS-sponsored study on sourcing Cloud-based services. The purpose of the study was to develop clarity on what organizations can do to successfully source Cloud services. The topic emerges as one of the most pressing issues for CPOs and CIOs as their organizations prepare to invest millions of dollars in Cloud-based services. Gartner, for instance, recently predicted that the public Cloud services market is expected to be more than $200 billion in 2016. The present study was commissioned at the behest of CPOs who are members of CAPS. In particular, the study focused on understanding the challenges of Cloud sourcing efforts, detailing the risks and their mitigation strategies and offering a framework for streamlining Cloud sourcing efforts of the organization.
We interviewed executives from six large firms that had annual revenues between $20 billion and $200 billion. Participant firms spanned several industry segments including technology, manufacturing, aerospace and defense, and energy. The interviews were a mix of on-site and telephone interviews. The target population was predominantly procurement teams and in some cases, these teams were complemented with members from the IT or legal groups. On-site interviews were typically conducted with a team of personnel that was closely involved in the Cloud sourcing process. Phone interviews were based on a single contact in two instances, and multiple contacts in IT and procurement groups in others. Finally, participating firms included not just Cloud buyers, but also Cloud suppliers.
The research effort began with a set of questions based on an extensive review of the research already published in this area. The questionnaire was also guided by feedback we received from several senior procurement managers. In addition, one of the authors participated in a CAPS focus group event to gather insights from participating companies. We traveled to firms’ locations to meet with teams of executives; firms also generously contributed documentation on a non-disclosure basis, on request. Our questions focused on several key areas, including an understanding of the current and future IT environment in the firms; understanding the key aspects behind supplier selection and performance monitoring in Cloud sourcing efforts; and assessing the risks and mitigation strategies of Cloud sourcing efforts across the different stages.
Backdrop of Cloud sourcing efforts
Organizations move their IT to the Cloud for one or more of the following reasons. On the internal side, they adopt Cloud to lower the cost of their IT infrastructure or to improve the ability to scale their business—often globally. On the external side, they may be forced to move to Cloud services by software suppliers that are increasingly migrating their on-premise solutions to the Cloud. In the process, organizations are discovering that sourcing Cloud services is complex—especially compared to traditional sourcing efforts—for several reasons.
First, for most large organizations, Cloud sourcing efforts are often carried out against large investments in an existing on-premise IT infrastructure that is maintained at a considerable expense. When compared to the existing on-premise infrastructure, creating a flexible, cost effective sourcing model for a Cloud infrastructure that may form the future IT infrastructure for the firm can be a challenge. This is not a short-term move and requires a carefully thought out strategy.
Second, firms need to balance the risks in Cloud sourcing efforts with the returns that the organizations can achieve by transitioning to the Cloud. These risks relate to data and information security, supply base management and management of cultural changes within the organization. Finally, risks differ across the phases of the Cloud sourcing effort through adoption, use and exit. Effective mitigation of these risks is critical to the value firms’ can derive from Cloud sourcing.
Third, Cloud sourcing efforts are made more challenging by an array of Cloud hosting models. These include: Infrastructure as a Service (IaaS), Platform as a Service (PaaS) and Software as a Service (SaaS). In addition, delivery models are also classified into public, private or hybrid Cloud models. Let’s look at them one at a time.
- In IaaS, the underlying IT infrastructure is sourced, including networking, storage, servers and virtualization.
- In PaaS, the firm sources the operating environment of the applications (in addition to IaaS).
- In SaaS, user specific applications are sourced.
In the words of one executive we interviewed, IaaS is like renting an empty apartment, PaaS is like renting an apartment with furniture and SaaS is like renting an apartment and additional services (e.g., cleaning and cable services) required by the user that can serve specific needs.
The three delivery models can be described as follows:
- A public delivery model is based on a shared infrastructure with logical separation of information.
- A private delivery model is based on a “dedicated private infrastructure” for the firm.
- hybrid model, as the name suggests, is a mix of public and private.
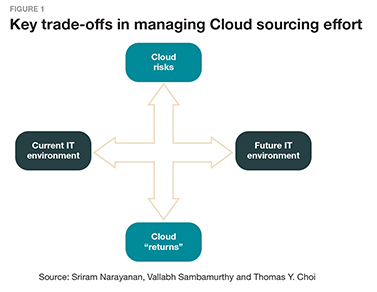
Figure 1 shows the importance of managing the trade-offs between the current and future Cloud infrastructure, and balancing the risk versus the value that may be derived. Adequate balancing requires organizations to have a portfolio of solutions around the IaaS, PaaS and SaaS models and the public, private and hybrid delivery models. Each delivery model brings its own set of key risks and benefits as well as challenges to managing the total cost of Cloud sourcing initiatives. For most firms, the increasing complexity of the Cloud solution portfolio, in parallel with the complexity of existing IT infrastructure, can make the transition to the Cloud very dynamic, difficult and resource intensive should Cloud transition efforts not be adequately planned and streamlined.
Finally, three groups of stakeholders need to work together for a successful sourcing of Cloud services. They are the user organization, the procurement organization and the IT organization. The concerns and views of each of these three groups can diverge and present significant risks for the organization in leveraging and deploying Cloud service solutions effectively. In particular, procurement managers need to be cognizant of these issues because they are likely to provide the interface between the buying firm and the Cloud services provider.
Risks in adoption of Cloud services
The risks in Cloud services are present across several key phases of Cloud sourcing. They can be quite unique to any organization and must often be carefully planned for. Figure 2 shows a framework to assess the risks of Cloud sourcing efforts, which can be divided into three phases—adoption, use and exit. These can be further divided into inter-organizational risks, such as with suppliers and risks within the organization. 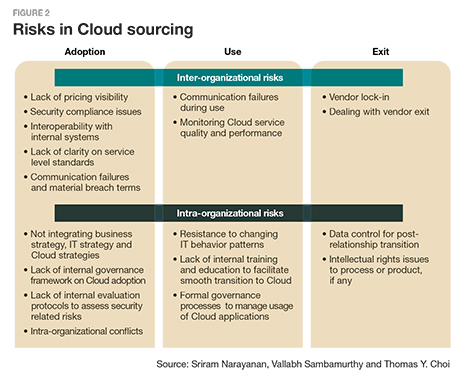
Price comparison tops the list of inter-organizational risks because it is often difficult to make clear apples-to-apples comparisons of the cost of Cloud solutions from multiple suppliers. That is because pricing is often a la carte and depends on usage levels of the service. Service level standards are also difficult to pin down, and thus are a source of risk. In particular, penalties on suppliers against service failures are among the most difficult to quantify. In addition, several of the participating firms in our research cited security compliance as an important risk. For instance, a Cloud service may need to comply with well-defined security standards at the industry level, such as ISO. It is important to note that the perception of security risks varies by industry. For example, firms in the defense industry felt security risk was more important than firms in some other industries.
Participating firms identified several internal risks when it comes to the adoption of the Cloud. They are: the lack of awareness of how the Cloud adoption fits into the firm’s overall IT and business strategies; the propensity to significantly customize the Cloud software (that fundamentally destroys the value proposition of cost); the lack of internal governance protocols and frameworks on how to select and adopt solutions and manage the transition to Cloud; and intra-organizational conflicts between units in the firm that are responsible for Cloud sourcing and use.
Setting internal governance processes on how the Cloud software is procured and the collaborative involvement of end user organizations is critical in this regard. Specifically, Cloud service procurement requires individuals from multiple disciplines to collaborate including IT, purchasing and the home function that uses the software. Incentives to procure and use the Cloud solution need to be appropriately aligned.
Focusing on risks related to the use of Cloud software, proactive communication is a key element of managing suppliers. These include formulating incident reporting protocols, service usage reporting and careful delineation of escalation protocols and resolution of potential conflicts that may arise during the engagement. Escalation-related protocols may be invoked for managing SLA adherence, failures in the delivery of service and incidences of security breaches.
Within the firm, the key use-related risk comes from managing requests for transitioning from an on-premise setting to a Cloud environment and the transition to the Cloud after a solution is chosen. Further, in transitioning to the Cloud, training and usability are key factors that drives the successful use of Cloud solutions.
Finally, an exit strategy needs to be considered. It is important to recognize that sourcing Cloud software involves significant switching costs. Buyers may be locked into a Cloud vendor, making exit difficult. Even worse is not being able to use the data quickly enough when the contract is terminated with a specific supplier. Firms must ensure early on, at the contractual stage, that they retain the right to their data should the contract terminate in the future.
Mitigating the risks of Cloud sourcing
A vast majority of external risks that organizations face when sourcing in the Cloud can be mitigated by contracts. In this context, a contract template needs to detail key issues that the organization must focus on, with particular reference to inter-organizational risks. Figure 3 illustrates the most important elements in a contract template.
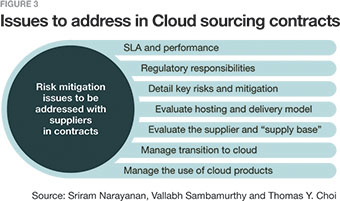
These include:
Technical and service performance parameters. These parameters specify how service level agreements are monitored and reported by suppliers. In some cases, organizations may consider the use of third party services to monitor performance.
Allocation of responsibility for regulatory compliance. Client organizations need to identify all the deal-specific regulatory compliance issues, such as The Health Insurance Portability and Accountability Act (HIPAA). These compliance requirements should be built into the contract.
Managing data security and integrity. Most firms have a portfolio of data types. Some are confidential and some are not. In that spirit, it is important for organizations to classify data into multiple types: (a) highly confidential; (b) confidential customer information; (c) confidential company information; and (d) public information. These classifications help prioritize aspects of the negotiation with regard to the nature of data that is protected and streamline the needs. In addition, it is critical to pursue and sometimes exceed industry security standards, depending on the level of information confidentiality.
A closely related aspect is the integrity of the data. Cloud suppliers use logical separation via encryption when using public delivery mechanisms. It is important to detail the scope and methodology of encryption to ensure that they conform to agreed upon industry standards. Further, procedures for unexpected system outages and the potential loss of data due to an outage need to be carefully detailed as part of the contract.
Pricing and payment. It is important for organizations to carefully scrutinize the pricing structure. In this regard, research on existing pricing protocols and pricing structures will be of significant benefit. Firms should compare pricing where possible by carefully normalizing the different service features among the vendors to ensure that they are comparing “apples to apples.” This will likely require a considerable degree of prior research into supplier pricing patterns. In addition, another aspect of pricing is related to managing potential changes in pricing. Conditions that could trigger pricing changes, and possible re-negotiation clauses, also need to be carefully detailed based on foreseen changes.
Mitigation of intellectual property risks. Firms that need to heavily customize the supplier’s code to meet their requirements need to consider intellectual property issues, such as who owns the modified code in the event of an exit, within the contract. In addition, where the firms use codes developed by the supplier, it is important to know the various third party codes within supplier products to mitigate consequent risks. For example, the use of modified open source code may come with restrictions on how protected the code of the firm is based on the nature of open source license.
Change management. Version changes in software solutions need to be carefully managed. Firms may request vendors to provide advance information on changes to software versions. The timeline for such information should be driven by internal process needs. A pre-approval process for changing software versions with the customer as part of the contractual agreement helps mitigate the risk of constant changes to the solution.
Exit Strategy. Exits can and do happen, for any number of reasons. A supplier may become bankrupt and exit a business or the relationship itself may terminate due to an acquisition or another business reason. With that in mind, an exit strategy should be devised in advance and then built into the contract with any supplier. Detailing it can be beneficial to maintaining continuity in the case of any eventuality in the buyer-supply relationship.
Successful sourcing on the Cloud: a process framework
Figure 4 shows a process framework that focuses on the key steps to successful Cloud sourcing. The framework divides the overall set of activities into two time points—pre-sourcing activities and during-sourcing activities.
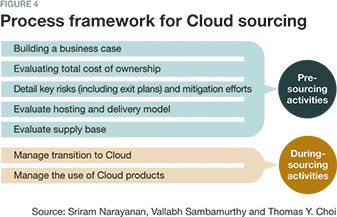
The most important step is building a business case for Cloud sourcing. The business case needs an appropriate tie-in between IT strategy, business strategy and Cloud strategy. The business case needs to be long-term and account for the envisioned future IT environment of the firm.
Second, to evaluate the total cost of ownership, organizations need to think beyond the cost of training and post-adoption to the hidden costs of transitioning to a Cloud solution based on the total time it might take to move existing physical processes to the Cloud and the consequent business disruption that might be caused. It is likely that such a move will not happen overnight.
Third, it is important to engage in a comprehensive risk assessment and mitigation effort. A comprehensive evaluation should take into account supplier risk posture, the delivery model risks and the enterprise risk posture. Creating templates that articulate each of these different aspects of risks can help facilitate their assessment. These templates need to be carefully matched to the existing realities of the firm’s governance structure. For example, in some firms, the IT governance can be centralized and IT acts as the key approver for all of the initiatives. In others, the business unit plays an important role, in the sense that IT decisions are decentralized at the business unit level. Accounting for these differences in creating the risk assessment framework is important.
Fourth, the firm must evaluate the Cloud delivery model and also take into account how the differing delivery models can lead to long-run cost reduction. Many organizations believe that a hybrid model that balances the security benefits of a private Cloud to the agility and economies of scale facilitated by the public Cloud is an ideal choice. Furthermore, the hosting model should be carefully detailed. In evaluating the hosting models involving SaaS, PaaS and IaaS (or a mix of these services), it is important to consider issues of inter-operability with not only internal systems but also with solutions provided by other suppliers.
Fifth, evaluation of the supply base should be done—where possible. This also means that any secondary suppliers to Cloud solutions may need to be evaluated and their risks understood.
Sixth, the transition to the Cloud should be carefully planned and executed. Some firms that participated in our research effort felt that there needs to be a protocol to evaluate acceptance testing of the software and its usability. Early pilot demonstrations are a good practice in this regard. Such demonstrations may alleviate cultural resistance to the use of Cloud software products.
Finally, it is important to manage the use of Cloud software. For our research, usage also includes monitoring the 37quality of services, setting expectations on the benefits that the adoption and usage of Cloud services will bring to the firm and training internal users and groups on appropriately managing Cloud sourcing efforts.
Managing the transition
Managing the transition to the Cloud is anything but trivial. It is important for senior management to recognize that Cloud sourcing is a business problem. In particular, the pursuit of Cloud technologies allows firms to fundamentally rethink the execution of organizational business processes.
Such an opportunity can help leaders in the firm realize the true potential of what the Cloud can do for their business. Thus, the effectiveness of Cloud sourcing is fundamentally reliant upon the management’s ability to create a portfolio of Cloud solutions that satisfy long-term business objectives.

Article Topics
Cloud News & Resources
Leveraging Artificial Intelligence (AI) to Transform Supply Chain Planning and Resilience Steady march into the cloud Technology Issue: Evaluate first, then apply Warehouse/DC Automation & Technology: It’s “go time” for investment Operate More Sustainably and Improve Logistics Performance by Moving to “The Edge” 31st Annual Study of Logistics and Transportation Trends Increase the Accuracy of Supply Chain Business Decisions Using Integrated Data Management and AI More CloudLatest in Logistics
Understanding the FTC’s ban on noncompetes UPS rolls out fuel surcharge increases U.S. rail carload and intermodal volumes, for week of April 20, are mixed, reports AAR Baltimore suing ship that crashed into bridge, closing port, costing jobs Intermodal growth volume remains intact in March, reports IANA Descartes announces acquisition of Dublin, Ireland-based Aerospace Software Developments Amid ongoing unexpected events, supply chains continue to readjust and adapt More LogisticsSubscribe to Logistics Management Magazine

Find out what the world's most innovative companies are doing to improve productivity in their plants and distribution centers.
Start your FREE subscription today.
April 2023 Logistics Management

Latest Resources